Development is driven by comprehensive policies and practices, verified by continuous automated scanning and validated through third-party penetration testing.


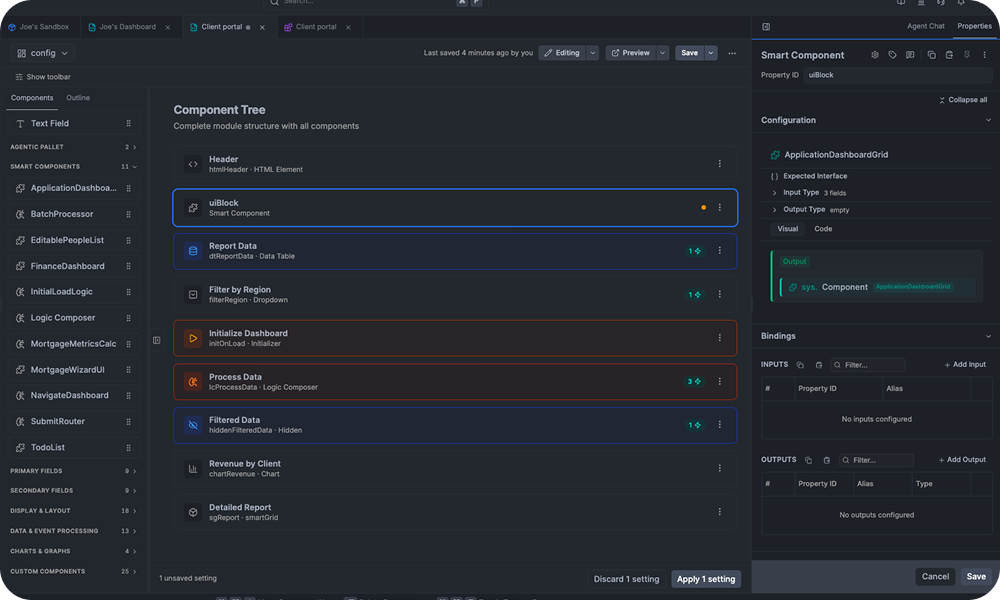
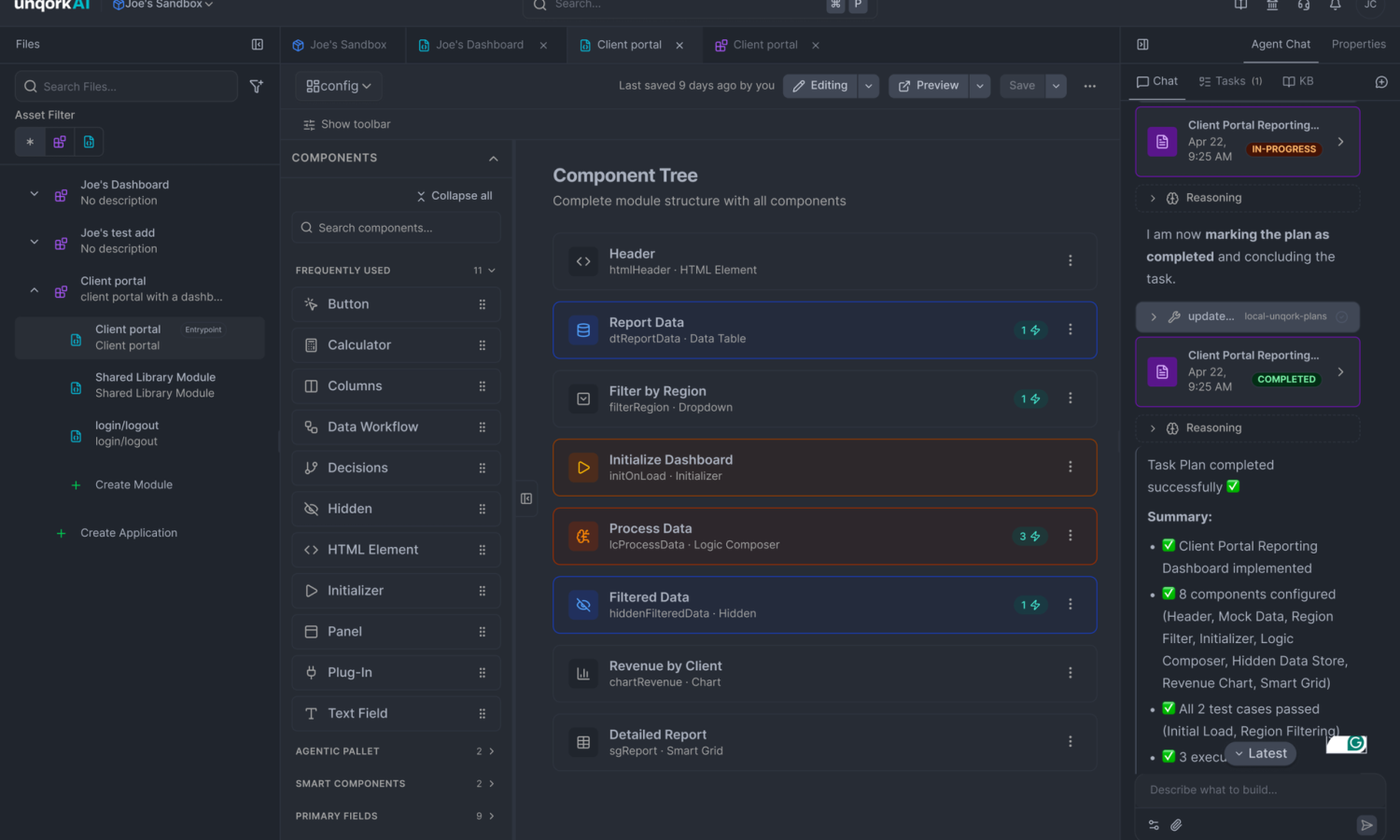
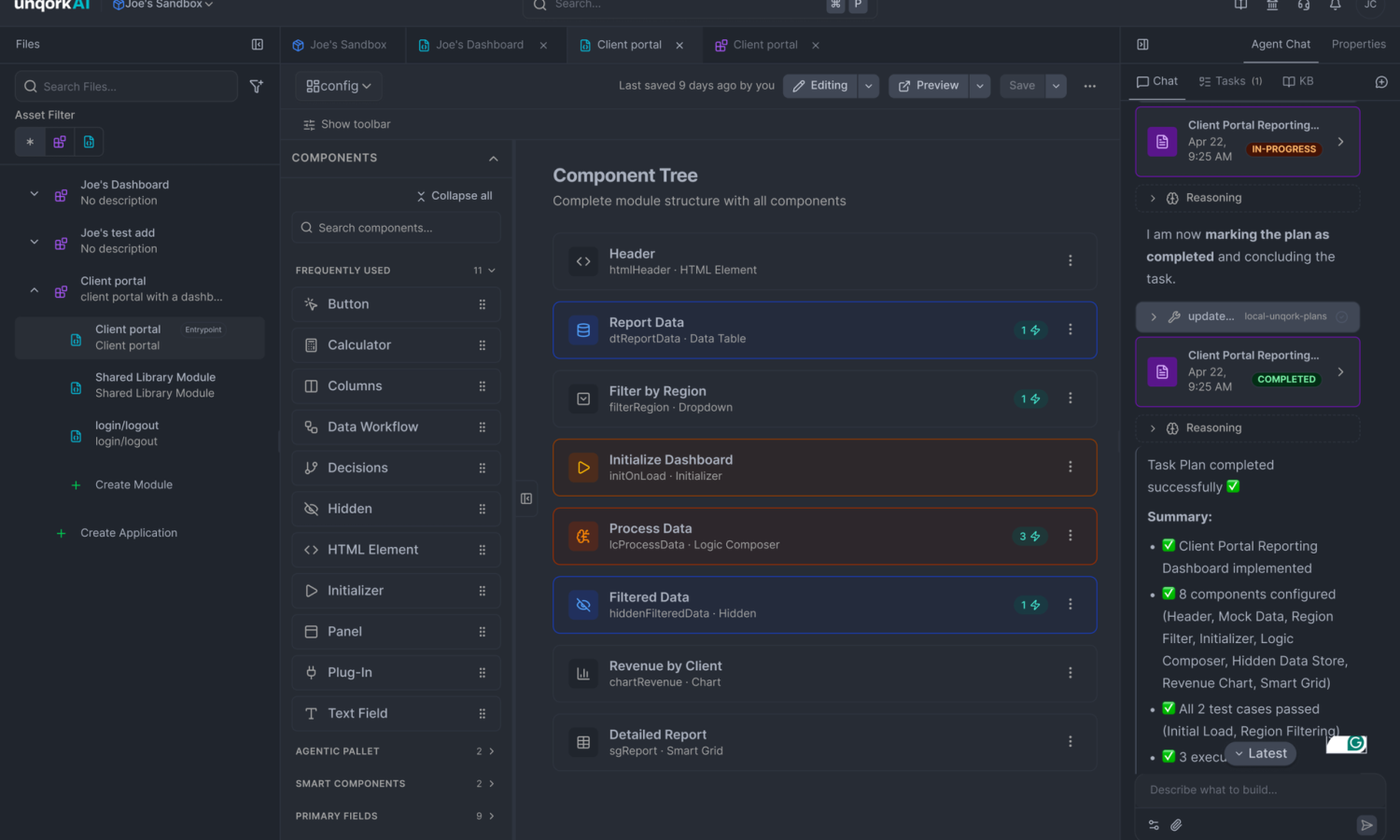
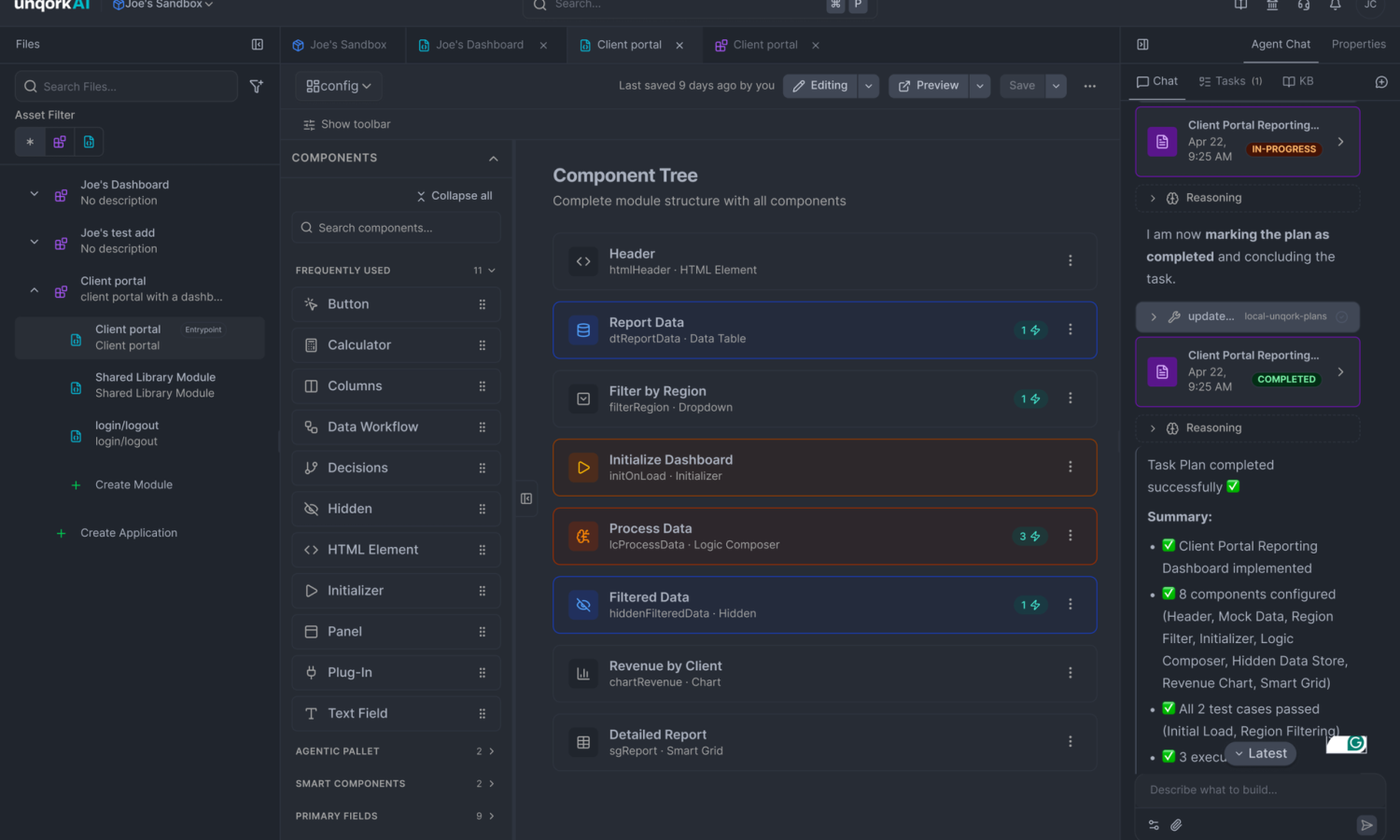
A component-based architecture enables application logic to be updated in isolation without risk to the broader app portfolio.
Data is protected with AES256 encryption at rest and secured in transit via TLS 1.2+ HTTPS using FIPS-validated cryptographic suites.
Enforce the principle of least privilege with RBAC applied precisely at both the individual module and component levels.